

The word OTP , standing for One-Time Password, has become very common in conversations regarding the security of online systems, particularly when discussing one-time password authentication methods.
One-time Passwords (OTPs) are unique passwords generated for a single session or transaction, embodying the concept of one-time password generation. They’re disposed of immediately after their one-time validity expires, addressing the question of what does one-time password mean in the context of enhanced security.
Speaking of regular passwords, did you know that the most popular password in use today is “123456”? Astonishingly, it is used by a staggering 17% of the Internet population, which underscores the vulnerability of static passwords.
Understanding what’s a 2FA code can be pivotal for users and organizations alike. 2FA employs both a password and a one-time code, usually an OTP, to verify a user’s identity. This dual-layer defense is highly effective, with studies showing that it blocks 99.9% of unauthorized attempts.
To answer that, let’s first see how regular password systems work: During signups, users create their passwords which they’ll have to memorize. This is quite different from how to implement OTP systems.
OTP systems, as the name would suggest, involve how to generate OTP. One-time passwords are a series of characters (letters or numbers) that are auto-generated and used only once for a single login session or transaction. This means users don’t own the passwords. For example, “20129” is an example of a one-time password.
At sign-up pages, addressing how to implement OTP verification, OTP systems automatically generate short passwords (passcodes) that are sent to users by email or text messages — with the help of white label SMS platforms . Users are expected to read and type in these passwords to confirm their identities. This process is crucial in understanding how to implement OTP verification effectively.
This OTP mechanism shields your systems from regular hacking techniques like phishing, password sniffing, man-in-the-middle attacks, and even replay attacks. In the context of how to generate OTP, these are created dynamically and offer an added layer of security. OTPs can be used in combination with static password systems, where they enable multiple-factor authentication for your websites and add another layer of security. This combined approach is a practical example of how to implement OTP alongside existing security measures.
99.9% of security attacks are blocked by multi-factor authentication, according to Microsoft. OTPs make multi-factor authentication possible. Static password generation is convenient for users, but people are often too careless with their passwords.
With multi-factor authentication, your password and username are not sufficient. The pin authentication is instantly sent to you via email or SMS, requesting you to further confirm your identity.
OTPs are safer and better because:
OTP systems, a key aspect of implement OTP strategies, function based on shared secrets between the user’s app or website and the authentication server. This is particularly crucial in implementing OTP authentication. Basically, when an unauthenticated user attempts to access the system, an authentication protocol on the network server automatically generates a series of characters or numbers (shared secrets). This process is integral to how to create OTP. The protocol does so using one-time password hash algorithms, which is a critical step in how to implement OTP based login systems
2FA (two-factor authentication) is a security method where two different forms of identification are required to access an account. Typically, this involves something you know (a password) and something you have (a device). A common form of the second factor is an OTP (One-Time Password), which is a temporary code sent to your device, often through SMS or an authentication app. While 2FA refers to the overall method involving two layers of security, an OTP is a type of code used within some 2FA systems to provide the second layer of security. Thus, what’s a 2FA code? It can be an OTP, but 2FA could also involve other methods like biometric verification. Essentially, what are 2FA codes? They are mechanisms that add an extra layer of security, ensuring that the person requesting access is who they claim to be. In summary, 2FA is the broad concept, and OTPs are specific tools used within some 2FA frameworks to enhance security.
Implementing 2FA (Two-Factor Authentication) from BSG involves a straightforward process designed to enhance security efficiently. Here are four key steps to implement 2FA from BSG:
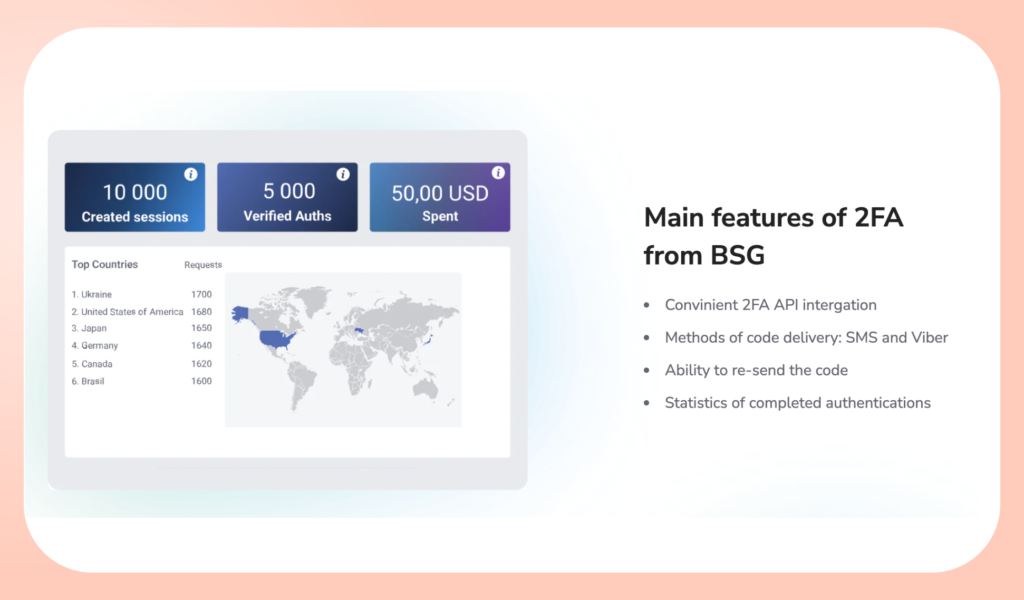
The main features of BSG’s 2FA solution are designed to boost both security and user experience:
This robust framework enhances security by requiring a second form of user verification and supports compliance with stringent data protection regulations like GDPR, making it indispensable for businesses in regulated industries.
Video here:
Apps that use OTP, demonstrating how to implement OTP, rely on a PIN and a microprocessor-based smartcard called a token to generate the numeric or alphanumeric one-time passwords. This mechanism is an essential part of the procedure to implement OTP authentication effectively. The combination of a PIN and a token encapsulates the process of how to create OTP.
What is OTP verification ? The actual numbers or characters of the one-time passwords, addressing how OTP is generated, are created using the Hashed Message Authentication Code algorithm, together with a variable parameter. Such parameters could be:
This process is fundamental to understanding how to create OTP. The OTP values have timestamps that last for seconds or minutes for greater security. When we discuss how does OTP authentication work, it’s important to note that the one-time password is sent to the user trying to gain access to the system. The same number and OTP generation algorithm are used by the security token on the smart card to match and validate the one-time password and the user.
If you’re logging into an online system that requires a one-time password (OTP), part of how OTP is generated involves it being sent to you via an SMS gateway (text messaging), by email, or through a dedicated application.
You’re required to input this code prior to finalizing your transaction online, which is a key aspect of how does OTP authentication work. However, the OTP code is sent to you on request, which is a crucial step in how to create OTP. The requested OTP should arrive almost instantly. In case your OTP doesn’t arrive in under a minute, there may have been temporary network issues or delays with your Internet service provider (ISP). You can request for another OTP to be sent to you.
Why is One Time Password safe? One-time passwords are not just safe but quite popular in the era where cyber theft threatens the safety of your infrastructure . Here are a few benefits of one-time passwords:
Since the start of 2017, Hackers have published about 555 million stolen passwords on the dark web, according to Cnet. Password theft is a huge weakness of static password systems. With one-time passwords, users have no ownership and so theft is almost impossible. How do you steal a password that is automatically generated at sign-up and only lasts 60 seconds to a few minutes? Really hard!
Short-term validity — expiration times:
As we’ve seen already, OTPs have a short life span ranging from a few seconds to a few minutes. Common attacks like phishing and password sniffing are really difficult to pull off on systems that have OTPs.
Strong passwords and good password habits are already a big problem for hackers. When you add an extra layer of security in addition to the password and the usernames, it presents a bigger challenge for hackers. 2 Factor authentication basically asks the question: “Are you who you say you are?”
Passwords like “abc123”, “Password”, “123456”, etc. are the most common passwords used by a whopping 24% of Americans . Weak and common passwords are a big problem for static password systems. A problem that OTPs have been able to fix. That extra layer of security with the OTPs ensures that your identity can’t be easily stolen. Do well to practice all good password habits regardless.
Like every good system, OTPs have problems too. Here are some of them:
The fact that users have to request for an OTP to be sent to users, requiring them to wait for an extra minute is a bit annoying. Users after taking the time to enter their passwords and usernames will still have to wait for these shortcodes.
The glory of OTPs lies in their short-term validity and auto-generation, which means hackers can’t intercept them. But, these codes are still sent via email or SMS. These channels are still somewhat vulnerable to high-level hackers who might just be waiting at the right moment.
Users are sometimes frustrated when codes arrive too late; having already expired while they wait. Sometimes the codes don’t arrive at all, and users especially in low bandwidth areas are obliged to request new OTPs over and over again. All this can be really frustrating to deal with.
In a later section, we’ll discover how to set up an OTP system; especially with regard to the necessary components. In general, OTP systems are more complex to set up and maintain, compared with static systems. The extra OTP requests and verification toolkits add to the bulk.

OTPs are generally used by brands that deal with sensitive user data. Some of these include
You must be wondering: “How do I get OTP verification for my app?”
OTP implementation is possible with several different technologies. Each technique brings its own trade-offs in terms of security, convenience, cost, and accuracy. The most common options are
Grid cards are credit card-sized plastic cards that fit into the user’s wallets. Printed on these cards are security grids (a matrix of random numbers and letters marked in rows and columns). The security grids can be used for SMS two-factor authentication .
How? Security grids can be auto-generated and sent confidentially to the users by email or SMS. Users then enter these numbers as one-time passwords, to identify themselves on systems that use this technology.
How does the OTP token work?
Security tokens are hardware devices capable of generating one-time passwords for security systems. Some of these tokens are PIN protected, assuring an extra level of security.
Smart cards are microprocessor-based hardware tokens also capable of generating one-time passwords using Hashed Message Authentication Code. They’re more advanced compared to regular tokens, providing stronger authentication, higher storage capacity, processing power, and ease of implementation.
Public Key Infrastructure (PKI) for OTP Strong Authentication
PKI technology provides one of the most comprehensive security with 2-factor authentication (2FA). In other words, they’re a more complex alternative to OTP systems.
PKI’s are also the most difficult mechanisms to implement, given the lack of corporate expertise in the technology. Certain vendors are offering a PKI-based solution as a service where enterprises don’t need to bother about key management.
OTPs are here to stay because they guarantee security in a way that static systems can’t.
Regardless of what technologies you choose for your projects, you will absolutely need an email or text messaging service that takes privacy and security very seriously. Get in touch with the BSG for all your messaging services/OTP needs.

